![Sponsored] Overwhelmed with How to Protect your Medical Devices from Cyber Threats? Time to Add Some New Tools to Your Toolbox | TechNation Sponsored] Overwhelmed with How to Protect your Medical Devices from Cyber Threats? Time to Add Some New Tools to Your Toolbox | TechNation](https://1technation.com/wp-content/uploads/2021/09/device-security.jpg)
Sponsored] Overwhelmed with How to Protect your Medical Devices from Cyber Threats? Time to Add Some New Tools to Your Toolbox | TechNation

Cyber Observer's Latest Release Provides New Visibility Into Cybersecurity Risk Posture | Business Wire

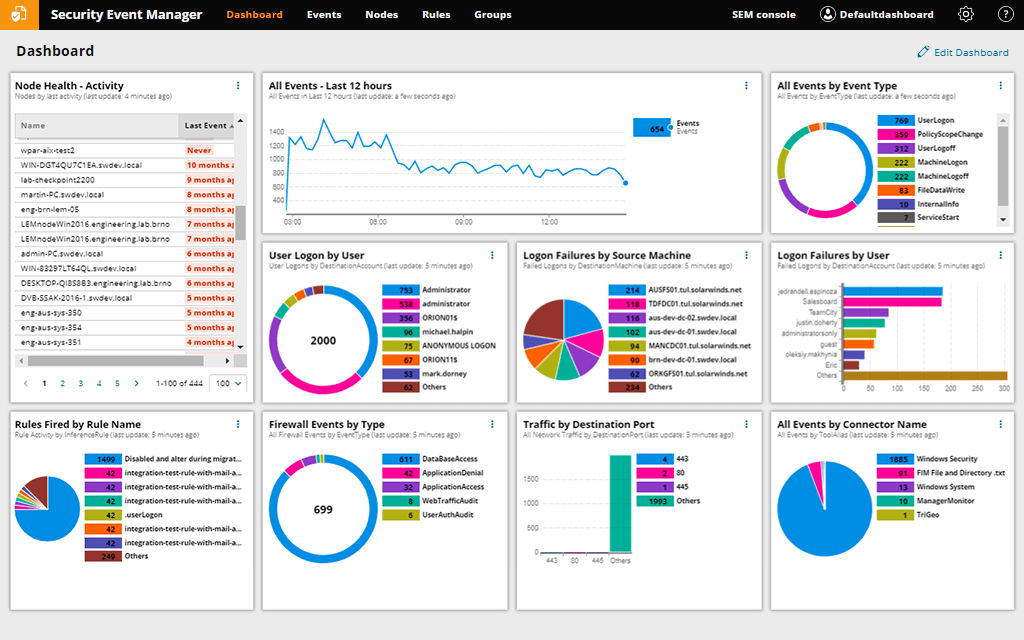
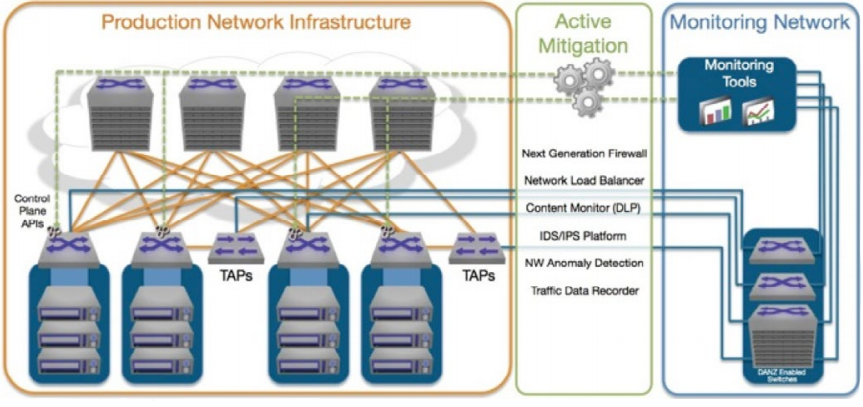
Top 3 Network Monitoring Tools - Cyber Security Blogs - Valency Networks - Best VAPT Penetration Testing Cyber Security Company - Pune Mumbai Hyderabad Delhi Bangalore Ahmedabad Kolkata India Dubai Bahrain Qatar
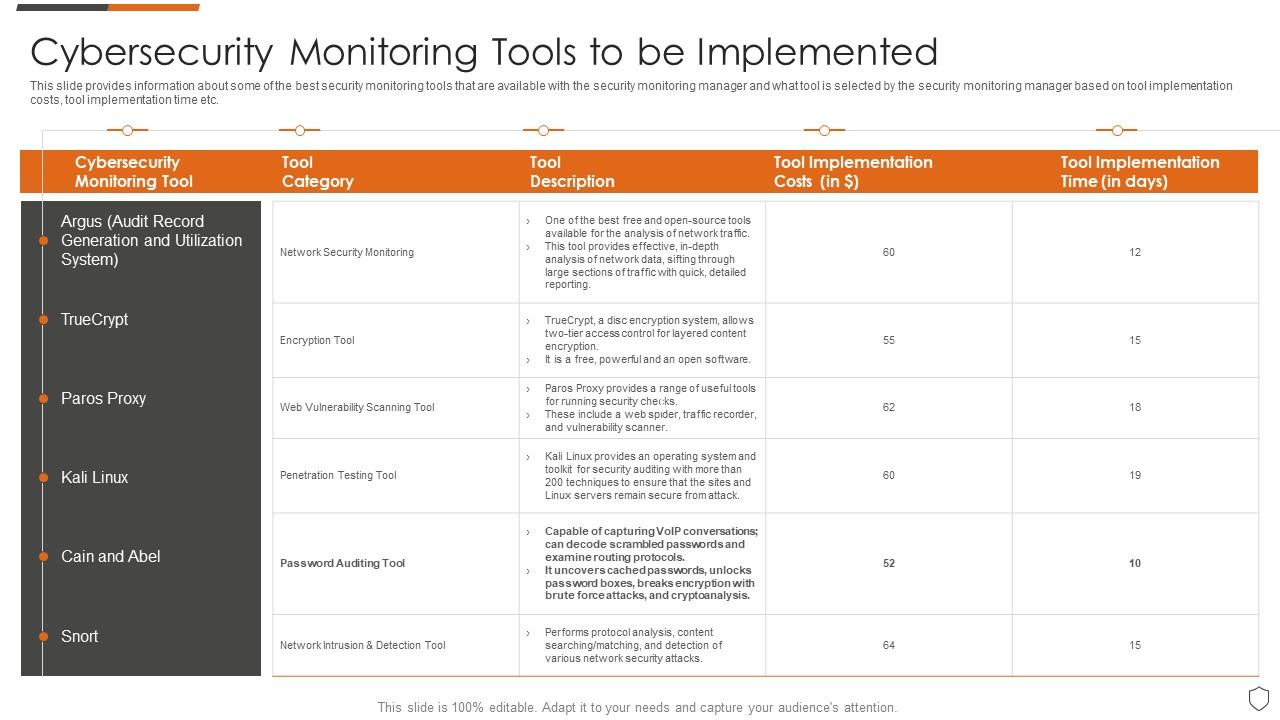
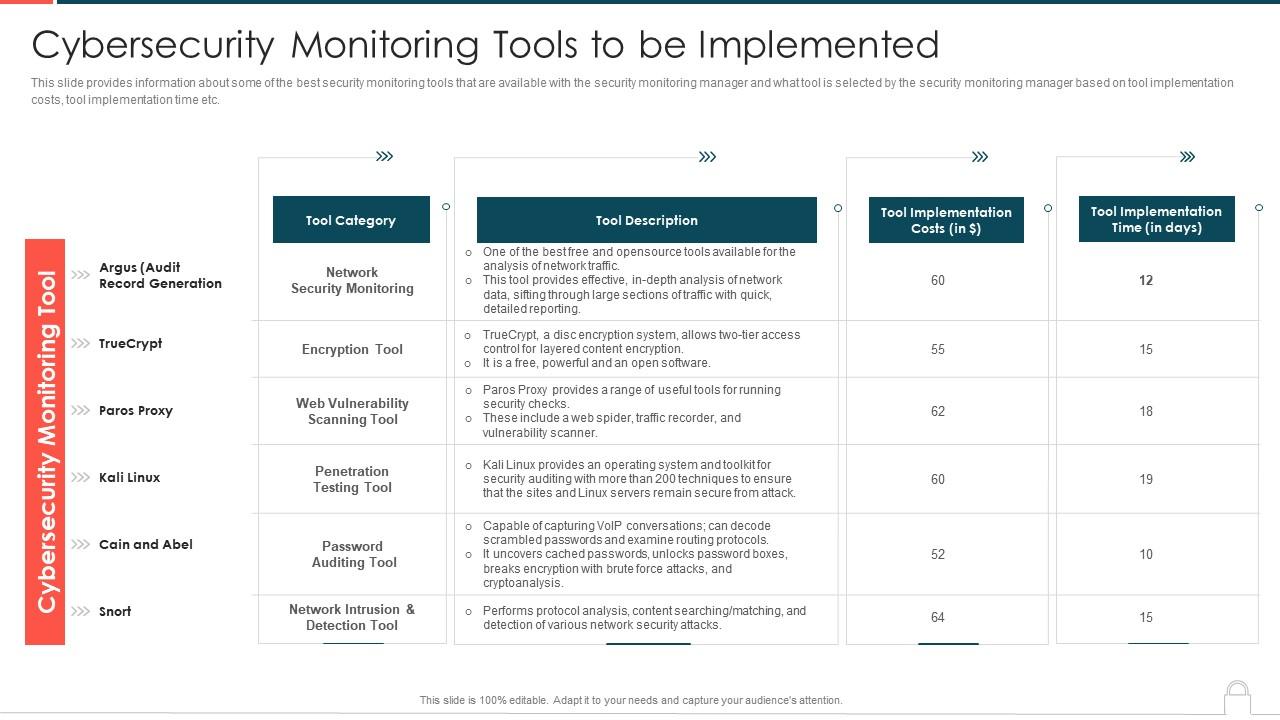
Cybersecurity Monitoring Tools To Be Implemented Ppt Powerpoint Presentation File Gallery | Presentation Graphics | Presentation PowerPoint Example | Slide Templates








![20 Top Cyber Security Tools in 2023 [Most Powerful Tools] 20 Top Cyber Security Tools in 2023 [Most Powerful Tools]](https://intellipaat.com/blog/wp-content/uploads/2021/06/Top-20-Cyber-Security-Tools-Big.png)